Having a comprehensive identity management solution is great but the real power comes when we integrate with other tools. Providing a safe channel for remote workers to access the company network is a particular challenge. Maintaining VPN certificates, users and passwords is a critical task that is in most organisations usually handle manually. This section is intended to highlight the relative ease to set up an Enterprise grade solution using FreeIPA and OpenVPN.
Server Keys and Certificates
FreeIPA includes a certificate authority which we can use to generate SSL/TLS certificates on the fly. When a host is included into the Kerberos realm a trust relationship is formed and the host is then able to request its own certificates via the service bus. Our VPN concentrator is already enrolled into FreeIPA so the command
[root@ipa ~]# ipa-getcert request -f /var/lib/certmonger/requests/server.crt -k /var/lib/certmonger/requests/server.key -r New signing request "20170222122747" added.
will generate the required keys which can then be used by OpenVPN. This process can be efficiently automated so the process of rotating keys becomes somewhat easy.
Client Keys and Certificates
If we do not wish to add a machine to the Realm fully, perhaps it is a personal laptop or is using an operating system incompatible with the enrolment process we will need to create an entry for our VPN client in the FreeIPA database so we can issue a certificate for it. After we create a Kerberos service principle for the client we then tell FreeIPA that we would like our VPN concentrator to be responsible for administering this principle.
Add host:
[root@ipa ~]# kinit admin [root@ipa ~]# ipa host-add --force hades.MacBook-Pro.local ------------------------------------ Added host "hades.macbook-pro.local" ------------------------------------ Host name: hades.macbook-pro.local Principal name: host/[email protected] Principal alias: host/[email protected] Password: False Keytab: False Managed by: hades.macbook-pro.local
Add VPN host to freeipa
[root@ipavpn ~]# ipa-client-install --domain=test.com --server=ipa1.test.com --server=ipa2.test.com --principal=admin --password=admin_password_ipa --mkhomedir
Autodiscovery of servers for failover cannot work with this configuration.
If you proceed with the installation, services will be configured to always access the discovered server for all operations and will not fail over to other servers in case of failure.
Proceed with fixed values and no DNS discovery? [no]: yes
Client hostname: ipavpn.test.com
Realm: TEST.COM
DNS Domain: test.com
IPA Server: ipa1.test.com, ipa2.test.com
BaseDN: dc=test,dc=com
Continue to configure the system with these values? [no]: yes
Synchronizing time with KDC...
Attempting to sync time using ntpd. Will timeout after 15 seconds
Successfully retrieved CA cert
Subject: CN=Certificate Authority,O=TEST.COM
Issuer: CN=Certificate Authority,O=TEST.COM
Valid From: Thu Feb 16 16:26:28 2017 UTC
Valid Until: Mon Feb 16 16:26:28 2037 UTC
Enrolled in IPA realm TEST.COM
Created /etc/ipa/default.conf
New SSSD config will be created
Configured sudoers in /etc/nsswitch.conf
Configured /etc/sssd/sssd.conf
Configured /etc/krb5.conf for IPA realm TEST.COM
trying https://ipa1.test.com/ipa/json
Forwarding 'schema' to json server 'https://ipa1.test.com/ipa/json'
trying https://ipa1.test.com/ipa/session/json
Forwarding 'ping' to json server 'https://ipa1.test.com/ipa/session/json'
Forwarding 'ca_is_enabled' to json server 'https://ipa1.test.com/ipa/session/json'
Systemwide CA database updated.
Hostname (ipavpn.test.com) does not have A/AAAA record.
Failed to update DNS records.
Missing A/AAAA record(s) for host ipavpn.test.com: 192.168.1.2.
Missing reverse record(s) for address(es): 192.168.1.2.
Adding SSH public key from /etc/ssh/ssh_host_rsa_key.pub
Adding SSH public key from /etc/ssh/ssh_host_ecdsa_key.pub
Adding SSH public key from /etc/ssh/ssh_host_ed25519_key.pub
Forwarding 'host_mod' to json server 'https://ipa1.test.com/ipa/session/json'
Could not update DNS SSHFP records.
SSSD enabled
Configured /etc/openldap/ldap.conf
No SRV records of NTP servers found. IPA server address will be used
NTP enabled
Configured /etc/ssh/ssh_config
Configured /etc/ssh/sshd_config
Configuring test.com as NIS domain.
Client configuration complete.
Add service:
[root@ipa ~]# ipa service-add --force client/hades.MacBook-Pro.local ----------------------------------------------------------- Added service "client/[email protected]" ----------------------------------------------------------- Principal name: client/[email protected] Principal alias: client/[email protected] Managed by: hades.macbook-pro.local
Add service host:
[root@ipa ~]# ipa service-add-host --hosts ipavpn.test.com client/hades.MacBook-Pro.local Principal name: client/[email protected] Principal alias: client/[email protected] Managed by: hades.macbook-pro.local, ipavpn.test.com ------------------------- Number of members added 1 -------------------------
We can now create client certificates for this client on the VPN concentrator machine.
[root@ipavpn ~]# kinit admin Password for [email protected]: [root@ipavpn ~]# ipa-getcert request -f /var/lib/certmonger/requests/hades.MacBook-Pro.local.crt -k /var/lib/certmonger/requests/hades.MacBook-Pro.local.key -N CN=hades.MacBook-Pro.local -D hades.MacBook-Pro.local -K client/hades.MacBook-Pro.local New signing request "20170222131252" added.
Along with the CA cert and the Diffie Hellman parameters the key and certificate can now be transferred to the client and used with any OpenVPN client such as TunnelBlick or Viscosity. OpenVPN does support Certificate Revocation Lists (CRL) but only from the local filesystem so a process would have to be put in place to generate this file.
[root@ipavpn ~]# grep plugin /etc/openvpn/server.conf plugin /usr/lib64/openvpn/plugins/openvpn-plugin-auth-pam.so "openvpn login USERNAME password PASSWORD"
We can use the common system-auth configuration so we make a symlink to the default location for OpenVPN pam plugin configuration.
ln -s /etc/pam.d/system-auth /etc/pam.d/openvpn
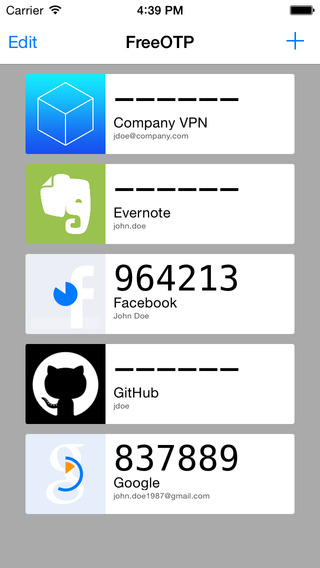
Using the Freeipa command line interface we can inspect the user that we want to connect via the VPN. We can see that it is enabled for OTP. Using a Cyanogenmod android phone with FreeOTP installed we snapped the QR code produced by FreeIPA and were immediately able to use it for authentication.
Annoyingly we were blocked by the OS from taking an actual screenshot of FreeOTP
[root@ipa ~]# ipa user-show Dmitriy.Korniychuk User login: dmitriy.korniychuk First name: Dmitriy Last name: Korniychuk Home directory: /home/dmitriy.korniychuk Login shell: /bin/sh Email address: [email protected] UID: 1014100000 GID: 1014100000 Account disabled: False User authentication types: otp Password: True Member of groups: ipausers Kerberos keys available: True
Using a completely standard client OpenVPN configuration with only one addition “auth-user-pass” to prompt for a password we are able to use OpenVPN to log into a network using password+OTP.
Leave a Reply